[DOWNLOAD PDF] https://ia600205.us.archive.org/10/items/icla-219/ICLA219.pdf
Submitted Anonymously Over Email
[DOWNLOAD PDF] https://ia600205.us.archive.org/10/items/icla-219/ICLA219.pdf
Submitted Anonymously Over Email
Sent in by a supporter; statement attributed to “the I.C.L.A.”.
On March 5th, 2023, the sky over Weelaunee Forest exploded and the screams of roughly a hundred people, diving from gas cans in terror, ripped through the treeline. In a matter of minutes, barely an hour, the casual Woodstock vibe of the South River Festival, cultivated and well-maintained over the previous day by the sheer concentration of upper-middle class hippies and bohemians, collapsed under the yoke of the Atlanta Police Department’s retribution. In those minutes, without having to move an inch, the entire political mass – over two hundred ravers, tourists, journalists, oogles, forest defenders, and children – migrated from a somewhat transgressive concert to a militarized cordon, the terms and limits of which had been set by squads and columns of vindictive pigs. The mood of the crowd shifted on reflex: from the short-lived euphoria of momentary triumphs to panics that drove them to flee wildly into the trees or back to camp.
As the hours passed and night approached, it was clear to at least a handful of us that the cops intended to wear us down by attrition. They had deployed a sequence of tactics that would successively shock-and-awe the crowd, siphon off the less radical elements by giving them a legal exit, then reinforce the parameter to cast a wide net for trapping potential evacuees. Whoever they could grab among the frontlines in the field were detained and charged with “domestic terrorism,” whoever found themselves stumbling towards the safety of the adjoining residential streets, unknowingly into the web of armed columns, were simply gassed and beaten. That was what they wanted.
Organizers, catapulted against their will and idealism into the role, worked feverishly and haphazardly towards secreting people to safety. An anxious throng of small kids and their parents were led by a few scouts through a pitch-black clearing to a caravan that shuttled them back to the other side of the city. The bulk of the crowd didn’t vacate so much as disappear in a disjointed free-for-all while the ancillary police lines were called back in the hours that followed.
For a time, the constant insectoid hum and clicks of the surveillance drones were the only clear and present danger for those who remained with us at camp, which felt more in service of indignity than our case files. By 5AM, all that remained of the crude siege were the pigs’ leftovers dotted along the main artery of the field and the glorious monument to wreckage in the packed parking lot, very tired and very grumpy. Our fear, anxiety, and rage – an accumulation that gave us urgency, community, and only a few squabbles over nearly thirteen hours – had given way to a more generalized sense of despair and fatigue, then an acceptance of uncertainty, a diffident resolve.
While the rest of the camp finally rested, there was silence. The untended embers of the bonfire went out and the dark, cloaked in mist, fell everywhere. “No light, but only darkness visible.” Faceless, nameless, and struck by the beauty of the looming pines and the dew-soaked needles under my boots, I felt free. I stretched my fingers out into the air to feel the soft breeze move through my hands, and I felt love. When the pig sets foot in the forest, on the contrary, the pig feels fear, hate, and confusion. For this reason, the pig was driven out and barred from the woods with much ease and little effort. This was, is, and will be the essence and spirit of Weelaunee.
What was a temporary retreat for me, at what has ultimately been its breaking point, has been a hard-fought home for many others in the past two and a half years. It has been lost, retaken, and lost again in perpetuity. This is a zone where defenders have attempted to flow freely between various modes of protest, occupation, and liberation, united by a singular strategic purpose but only an incidental sense of political direction. It’s for this reason that the forest has served as a semi-stable nexus for clandestine organization and its concrete defense a centrifugal force in the development of clandestine work on a countrywide scale.
As some people have noticed Sprout Distros website appears to be down. An archive of the catalog page from February is available here but if you’re good searching the Internet Archive manually or know exactly what you’re looking for you can look through all their upload categories here.
What id really like to take this chance to do though is to encourage people and groups to create their own public digital zine archives so that theres less reliance on one Big Zine Site that can disappear or be taken down relatively easily. You can use a noblogs or blackblogs page to not just host the pdfs but also set up links and announce new things like Haters Cafe 1312 Press, Ungrateful Hyenas. Or skip the webpage part and just upload to Internet Archive either anonymously (make a throwaway account then delete it) or regularly like Perfect Disorder Press and Fugitive Distribution but just be aware the Archive people don’t claim to be radical aligned and can do shit like put pro Palestinian stuff in the “fringe” section. True Leap Press makes posts featuring specific zines or larger collections, this is another model to consider. Sites dedicated to other things also have zine pages/sidebars like the ones on Scenes or Puget Sounds Anarchists. There are many options and I really encourage people to explore them soon on their own time rather than only after something bad happens and you’re scrambling for alternatives.
UPDATE FROM SPROUT DISTRO:
site is now back online. it was just a temporary issue. 🙁
Submitted Anonymously Over Email
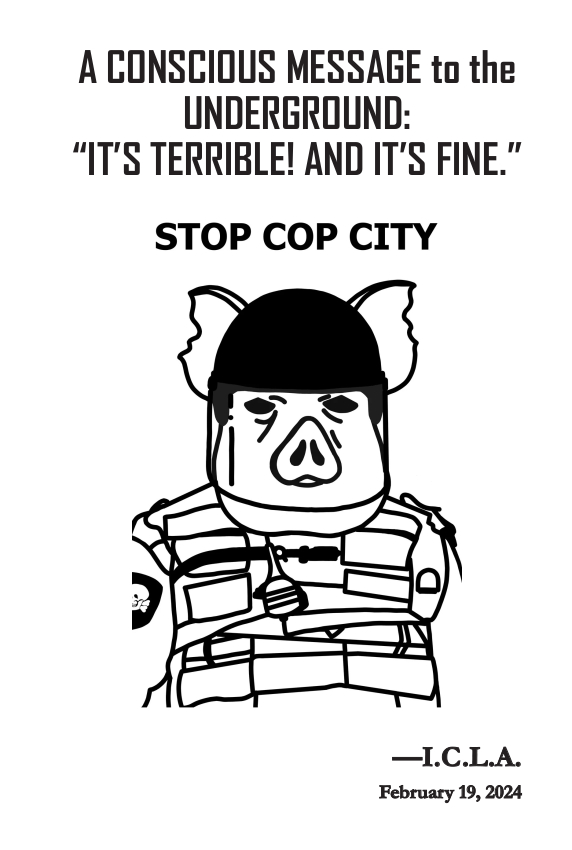
“They paid 25 million dollars”
Submitted Anonymously Over Email
“it is no longer enough to liberate animals from abuse whilst causing the scum that abuse them no bother. for that reason, we fucked up a dairy parlour as much as we could and hope the farmer had an absolute nightmare of a morning when they woke up.
every single one of the milking hoses were cut, as was all the iodine pipes and the air compression pipes that produce suction to milk the cows. the touchscreen computer that controls the whole system was broken, connectors cut and screen smashed.
in the dead of night, with accomplice cows mooing to cover the sound of destruction, we fight back against the capitalist system that commodifies cows as milking machines.
“we’ll be the burning rage
of a dying planet
it’s not too late
this is not the end.”
to jack in atlanta. fire burns in our hearts. the world keeps fighting.
some anarchists.”
From Unoffensive Animal
two of the videos broke while downloading/uploading.
Over the past few days the administrators have cleaned up some rough edges of the site:
– the submissions page and the sidebar now has more relevant information regarding internet security and image/video submission. (espiv files, whonix documentation, more detailed instructions on the submissions form)
– the drop down menu headers when clicked link to their own page containing the same information as the dropdown
– we are attempting to find a way to host embedded video for ease of uploading/viewing
– we have explored a few options (up to and including porn websites) and found that the only reasonable options are mastadon [https://kolektiva.social/@scenesfromtheatlantaforest] and tumblr. [https://scenesatl.tumblr.com/] ( we have created both <3 tumblr banned us)
the tumblr uses an RSS feed
and the mastadon is a plugin built into noblogs (thank you R & autistici inventati !!!! <3<3<3)
we have yet to understand entirely how the videos might work so below we are going to upload a tiny cat video to test.
videos have been a difficult hurdle
Thank you all! <3
A recent text outlining a path for developing action capacity concludes that “studying the vulnerabilities of domination” also needs attention. If a capacity for destruction is present, then the question naturally arises of how to aim it so that this destruction hits where it hurts. Let’s imagine what such an approach might entail by turning our gaze to a central pillar of global power and counterinsurgency: the U.S. “defense industry.”
Anarchists and other rebels based in the U.S. are well-placed to strike at its war machine—the ’60s saw a prolonged social upheaval driven primarily by this objective, and in the many years since, anarchists here have occasionally moved beyond opposing war to attacking it. The current genocide in Palestine has heightened social tensions against U.S. militarism, though the actions of anarchists in this moment have mostly had little impact on their targets and not contributed much to the popular imaginary of how militarism can be attacked. What could equip anarchists to carry out more significant strikes, to hone a quality of action that goes beyond the symbolic? To this end, the proposal put forward by “Fragments for an Insurgent Struggle Against Militarism and the World that Needs It” deserves discussion: to focus on well-conceived attacks that target vulnerabilities in the production and infrastructure of war.
The production of war starts here: the U.S. is by far the world’s largest arms exporter. Of SIPRI’s “Top 100 Arms-Producing and Military Services Companies,” 42 are based in the U.S., accounting for 51% of total global revenues. Most visible are the factories that churn out arms, ammunition and other war equipment. Less visible are the supply chains that transform raw materials into the components the factories need (production stage supply chains) or transport the finished product into the hands of States (distribution stage supply chains). “Fragments for an Insurgent Struggle…” proposes to focus destructive attention on the upstream supplier bottlenecks inherent in high-tech production, an industry “dependent on numerous expensive and difficult-to-obtain resources,” rather than on the well-secured assembly plants:
Arson attacks on the vehicles of arms companies and their suppliers, as well as on the vehicles of the logistics companies that transported their war material, etc., as well as a perhaps even larger series of paint attacks on the headquarters of these companies offered, and still offer, a militant perspective of intervention in war production. And yet: it would be news to me that supplies to the war fronts ever came to a standstill in the process. The interruption of production was too minor, the sabotage of logistics too insignificant. Nothing that could not have been made up by an additional night shift. And the financial damage? Well, let’s say that the management of these companies make calculations in other dimensions.
It is by no means my intention to talk down these attempts at intervention, to discourage people from attacking even when the enemy seems overwhelming and one’s own room to maneuver seems too small in comparison, one’s own resistance too insignificant. None of this is a reason for me to refrain from attacking. Rather, I think it is worthwhile to reconsider established strategies from time to time and, if necessary, to revise them when it becomes apparent that one’s actions within them are largely ineffective or becoming predictable.
The world’s largest defense contractor, Lockheed Martin, saw its annual revenue drop by 8.9% between 2021 and 2022 due to supply chain constraints (in other words, it couldn’t produce $6 billion worth of weapons). Of the 41 other U.S. companies in the “Top 100,” 31 also saw their annual revenue decline for the same reason. By identifying the specific supply chain bottlenecks that are already severely hampering these leviathanic entities, it becomes possible to exacerbate shortages in a way that actually impacts weapons production.
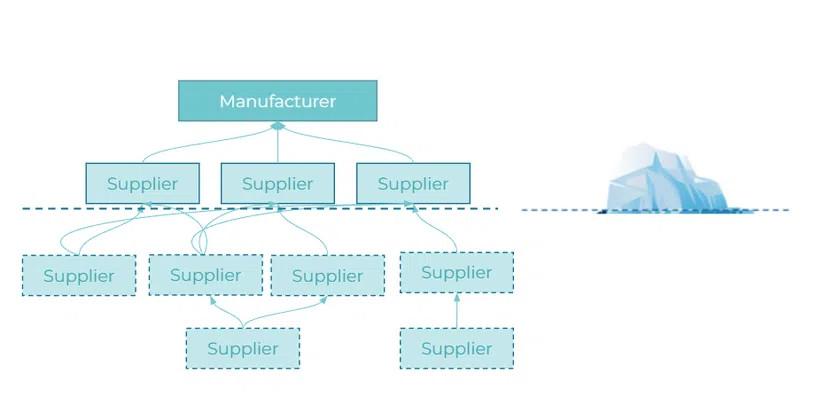
Supply chains consist of “tiers” and look more like a network than a linear “chain.” First tier suppliers directly supply a company like Lockheed Martin, second tier suppliers supply the first tier, and so on. The average U.S. aerospace company relies on about 200 first-tier suppliers, and the second and third tiers involve more than 12,000 companies. Irreplaceable suppliers are called “sole-source,” and are often present at all tiers. As one engineer recently warned in the trade press, “Dassault has five thousand suppliers for its Rafale, and all it takes to block everything is for one to get stuck.”
In addition to supplying product components, supply chains must also provide specialized factory machinery. For example, the production of the machinery required for the microelectronics (semiconductors) used in virtually all military technology is a severe bottleneck causing shortages in this sector. In February 2022, the Department of Defense (DoD) released an action plan for “Securing Defense-Critical Supply Chains” which warns that “the high-tech company ASML (Netherlands) is currently the sole-source for extreme ultraviolet (EUV) lithography tools that are required to mass produce semiconductor die in technology nodes below 7nm1. Such consolidation increases sole-source risk in the global microelectronics supply chain.” ASML produces only about 40 machines per year (each taking 12-18 months and involving more than 1,000 first-tier suppliers). They have a $50 billion backlog and their closest competitors are a decade behind EUV technology.
All supply chains have bottlenecks, and most have “single points of failure,” it’s just a matter of locating them. The tools to gain this visibility are included in the field of “supply chain risk management”—our enemies are publishing much of this research. The same DoD action plan describes “persistent sub-tier2 supply chain vulnerabilities, from raw materials and chemical shortages to critical subcomponents produced by fragile suppliers.” It goes on to provide a high-level overview of supply chain issues for “areas in which critical vulnerabilities pose the most pressing threat”: missiles, batteries, castings, microelectronics, and critical minerals.
More recently, for the first time in its history, the DoD released a “National Defense Industrial Strategy” to provide a roadmap for “developing more resilient and innovative supply chains.” Their plans are not infallible—one advisor describes the document as lacking “a focus on long-term solutions to supply chain issues that have plagued the defense industry.” Equally interesting are the publications of RAND’s National Security Research Division, especially those of its National Security Supply Chain Institute. Continue reading “Developing Incisive Capacity: Making Actions Count”
People use rise up under the impression that they wouldn’t cooperate with law enforcement but 8 years ago they buckled under pressure and handed over info to the FBI. (The warrant canary worked and tipped some people off but riseup’s later public statements undermined that) We don’t all know how we’d act under threats of imprisonment but many people counted on their explicit promise of non cooperation and they justified breaking that promise instead of admitting the fuckup.
If you choose to keep using rise up just be aware of this. if it’s a dealbreaker consider alternatives. Some are listed at https://blackblogs.org/policy/
Scenes admins have been brave enough to make a public non-cooperation promise that there’s no reason to believe has been broken so far. The cases above suggest that if anything did happen we should examine the warrant canary and other hard evidence over possibly coerced explanations after the fact if there are inconsistencies. (however this does not mean we should immediately accuse them of snitching if things don’t add up)
True safety may not be possible in this world but let’s do what we can to keep each other informed on the way to preventing cop city from ever being built. or burnt immediately upon completion 🙂
P.S. Protonmail also complies with cops and has specifically done so against anticapitalists. https://techcrunch.com/2021/09/06/protonmail-logged-ip-address-of-french-activist-after-order-by-swiss-authorities
++++++++++++++++++++++++
Below are quotes from https://web.archive.org/web/20220826163958/https://riseupsnitched.com/
On November 16, 2016 Riseup.net’s warrant canary expired and was not renewed. In the months that followed the company issued several tweets, one cryptically trying to offer reassurance, another more specifically asking for calm.
No specifics were given until February 16, 2017 when Riseup.net issued a statement explaining their silence. They confirmed the worst, stating:
“After exhausting our legal options, Riseup recently chose to comply with two sealed warrants from the FBI, rather than facing contempt of court (which would have resulted in jail time for Riseup birds and/or termination of the Riseup organization). The first concerned the public contact address for an international DDoS extortion ring. The second concerned an account using ransomware to extort money from people.”
…
While they may have not cooperated with the NSA, this is a distinction without a difference. Is anyone concerned about cooperation with the NSA and not concerned about cooperation with the FBI? And in case they want to get away with saying that is technically true, the rest of the statement throws that right out the window.
“We are not working with any government agency. We have never simply handed over information when requested, and for years have had a no logging policy. We have fought and won every time anyone has tried to get us to give up information. We have never turned over any user data to any third party, fourth party, fifth party or any party.”
Each one of these sentences is so wholly incompatible the sentence “Riseup recently chose to comply with two sealed warrants from the FBI” that any attempt to make them both true renders words themselves meaningless.
…
What Should Riseup.net Do?
In short, probably dissolve. [administrative note: please do not dissolve] This is the remedy they prescribe for themselves when they say “We would rather stop being Riseup before we [work with the FBI]. Remember, this is not a one-time regrettable mistake. In the years that followed they neither expressed remorse of any kind, not updated their promotional material or contracts to give their users a more accurate view of what they can expect.
Short of that, updating their materials to reflect the truth, that they have worked with government agencies, have handed over information when requested would be a good start.
Submitted Anonymously Over Email
Over the past 6 weeks, Lockbit 3.0’s ransomware has taken offline many government services within fulton county georgia usa.
An international multi-agency effort named “Operation Cronos” seized the original domains for Lockbit 3.0, while arresting, or sanctioning, a few alleged affiliates.
The Lockbit 3.0 administration has signed these links with these pgp keys and released a statement to vx-underground.
The new lockbit website contains a timer countdown for the release of fultoncounty dot gov data that was extracted during the ransom attack.
The deadline is: 29 Feb, 2024 13:49:36 UTC
POST:
lockbit3753ekiocyo5epmpy6klmejchjtzddoekjlnt6mu3qh4de2id.onion/post/hzhFgPB0IMHmNjwa65da5f32cbbec
New domains of the main Lockbit 3.0 blog:
lockbit3753ekiocyo5epmpy6klmejchjtzddoekjlnt6mu3qh4de2id.onion
lockbit3g3ohd3katajf6zaehxz4h4cnhmz5t735zpltywhwpc6oy3id.onion
lockbit3olp7oetlc4tl5zydnoluphh7fvdt5oa6arcp2757r7xkutid.onion
lockbit435xk3ki62yun7z5nhwz6jyjdp2c64j5vge536if2eny3gtid.onion
lockbit4lahhluquhoka3t4spqym2m3dhe66d6lr337glmnlgg2nndad.onion
lockbit6knrauo3qafoksvl742vieqbujxw7rd6ofzdtapjb4rrawqad.onion
lockbit7ouvrsdgtojeoj5hvu6bljqtghitekwpdy3b6y62ixtsu5jqd.onion
Submitted Anonymously Over Email
In the wee hours of the night during the week of 2/18, some feral flying forest squirrels descended upon a precinct in the heart of Brooklyn. With caution and courage, they left the scene quickly, leaving behind the sound of escaping air and blood red lettering on the side of two NYPD buses reading;
“For Tort”
10 NYPD vehicles were left with punctured tires.
As these vessels are primarily used to cage and transport prisoners, protestors, and those who live in friction with genocide and empire, it is clear that these vehicles needed to be taken out. But there are many more… Stay sharp, fellow beings of the forest! Our grief and rage are hard and heavy, but there are openings where we can hold it as a stone to sharpen the claws we have.
Viva viva Tortuguita!
Submitted Anonymously Over Email
On the evening of Sunday, February 25th, we, along with around 80 others gathered in downtown Tuscon to act against the construction of Cop City and in solidarity with the resistance to the Mountain Valley Pipeline. The demonstration was short and required less than 100 people. Within minutes of departing, the crowd vandalized and smashed all of the windows at two banks near Presidio Plaza, Wells Fargo and PNC. The former was targeted for its support of Cop City and the latter for its support of the Mountain Valley Pipeline. We briefly stopped at the courthouse, writing slogans and Tortuguita’s name, before disappearing into the night.
It was obvious that we took the police completely by surprise. The Tuscon PD underscored their incompetence by arresting random passers-by and failing to respond meaningfully in any way to the demonstration.
Actions like these are easy to replicate. We are ordinary people with ordinary skills; slightly organized, with a bit of audacity.
We commend the efforts of those in Scottsdale the following day at Nationwide’s regional Headquarters, those who locked-down at the mansion of regional executives, as well as the autonomous actions of all those who targeted and will target Nationwide and their subsidiary offices in Tuscon, Santa Cruz, New York, and other cities around the country.
Regarding the recent raids and arrest in Atlanta, we hope that this weekend serves as a reminder to both the public and the circus of federal and local agencies targeting the movement: the tenuous we-got-our-man assurances of Schierbaum and his department will not fool anybody. Like our friends, their enemies are everywhere.
COP CITY IS EVERY CITY
COP CITY WILL NEVER BE BUILT
Submitted Anonymously Over Email
 [ PDF DOWNLOAD ]
[ PDF DOWNLOAD ]
Submitted Anonymously
Found On Archive.org
Forest-Service-out [DOWNLOAD VIDEO]
Early on the morning of Saturday February 24th a subsidiary of Nationwide Insurance Company was attacked in Santa Cruz, CA. Their locks were glued shut and messages were spraypainted on their doors and walls. Fuck Cop City, it will never be built.
Submitted Anonymously Over Email
On the night of Friday, February 23rd we attacked three subsidiaries of Nationwide insurance in Tucson, Arizona, smashing their windows and vandalizing their buildings. We were able to do this easily and quickly with only a small group of friends. It was easy, fast, and brought us great joy. We write this hoping it raises your spirits as well.
This action is something that can be replicated any night, in any city. The continued work on cop city in Atlanta is only possible due to the support of Nationwide insurance and their many subsidiaries, and these same companies allow for the proliferation of militarized police projects everywhere.
We believe every supporter of cop city and anything like it must be destroyed completely, and we know there is a whole world fighting with us. Our enemies are everywhere, but we are not deterred by the long list of targets. We know the forest is everywhere, and most importantly we are everywhere.
To the many foot soldiers and bureaucrats of the genocidal police state we have only to say: you can’t hide, we are going to find you and we will destroy you. You cannot escape your complicity no matter how small. We do not care if you hide behind fortresses, walls, security guards, or the power of the state, these illusions will never protect you. Not only will we attack you we will attack everything within the walls of your fortress, everyone you associate with, and everything you think keeps you safe.
We are undeterred by your repression, and we will not stop until everyone is free.
For Tortuguita, for Palestine, for abolition, for total liberation,
For the sugauros and every moment we have together,
We’ll never stop fighting,
-Some Anarchists
Submitted Anonymously Over Email
As some of you may be aware “tucson arizona” is a us colonial outpost on the traditional homelands of the Tohono O’odham people. Many O’odham are largely confined to a nearby reservation under increasingly high-tech surveillance & violent border policing with high rates of poverty.
How Border Patrol Occupied the Tohono O’odham Nation
https://inthesetimes.com/article/us-mexico-border-surveillance-tohono-oodham-nation-border-patrol
Some quotes:
“Tohono O’odham aboriginal land, in what is now southern Arizona, historically extended 175 miles into Mexico, before being sliced off — without the tribe’s consent — by the 1853 Gadsden Purchase. As many as 2,500 of the tribe’s more than 30,000 members still live on the Mexico side. Tohono O’odham people used to travel between the United States and Mexico fairly easily on roads without checkpoints to visit family, go to school, visit a doctor or, like Estevan, a traditional dancer, perform ceremonial duties.
But incidents of U.S. Customs and Border Protection (CBP) aggression toward members of the Tohono O’odham Nation have become increasingly frequent since 9/11, as Border Patrol has doubled in size and further militarized its border enforcement. In 2007 and 2008, the United States built vehicle barriers on the Tohono O’odham Nation’s stretch of the U.S.-Mexico border, and restricted crossings.”
“the Tohono O’odham Legislative Council passed a resolution allowing CBP to contract the Israeli company Elbit Systems to build 10 integrated fixed towers, or IFTs, on the Nation’s land, surveillance infrastructure that many on the reservation see as a high-tech occupation.”
“Amy Juan and Nellie Jo David, members of the Tohono O’odham Hemajkam Rights Network (TOHRN), joined a delegation to the West Bank in October 2017 convened by the Palestinian organization Stop the Wall. It was a relief, Juan says, to talk “with people who understand our fears … who are dealing with militarization and technology.””
“Estevan is far from the only Tohono O’odham from Mexico to say they have been deported, although there has not been an official count. The Supreme Council of the O’odham of Mexico — which represents the Tohono O’odham who live on the Mexican side of the border — made an official complaint to the Tohono O’odham Nation’s government in May 2018, saying the Nation was “allowing the deportation of our people from our own lands.”
Some members of the Nation, such as Ofelia Rivas, of the Gu-Vo district, have long contended that the Legislative Council is too cozy with Border Patrol.”
Submitted Anonymously Over Email
“We are not special. Our skills are not overly technical or advanced, and our tools are simple to acquire. If you are reading this, you are capable of doing what we do.”
While I agree with this sentiment, the reader is left with many questions about how to develop such a capacity for action, even if they are motivated. What exactly does it take to not get caught carrying out heavy actions like arson? This is especially important in the long run; not getting caught for a single arson is one thing, but being able to continue carrying out attacks in the face of heightened repressive attention is quite another.
For anyone who wants to carry out actions like this, but isn’t doing so yet, I’ve sketched an outline of the steps I think are necessary to sustain hard-hitting attacks on domination (limited to the topic of “operational” considerations, i.e., acquiring skills). This brief outline is intended to orient you and provide a “learning path” — each step has recommended reading that actually goes into the appropriate amount of depth on the subject. Use the Tails operating system to visit these links, which runs from a USB drive and leaves no trace on your computer. What I’ve written here is by no means definitive, and I hope to spark a dialogue about any operational aspects I may have neglected, as well as anything outside this scope that is important for sustaining and intensifying the capacity for action.
For anyone who doesn’t already have an action group, deciding who to act with is the first obstacle to overcome. I prefer to act in groups of two or three; it’s easier to maintain a high level of trust and agility with just a small handful of people. Most actions don’t require more than three participants, and when they do, action groups can collaborate. I prefer not to act alone because some aspects of actions are less risky when there are at least two people (for example, having a lookout).
In deciding who to act with, there is a tension between flexibility and consistency. Acting in several different configurations allows you to develop trust and experience with more people, which makes you more resilient in the face of arrests, burnout, or interpersonal splits. On the other hand, acting in a more consistent configuration can make it easier to develop a higher capacity for action in a shorter period of time.
Action groups only form because someone takes the initiative to propose them to a comrade with whom they want to deepen affinity and trust.
Deciding who to approach in your network should be based on a sense of affinity between you, as this will determine what the action group decides to focus on. Affinity means sharing analysis, discovered through getting to know each other, that leads to prospects for action. It means knowing that you share goals and want to act in similar ways to pursue them.
The long-term exploration and deepening of affinity across a network, beyond a specific action group, opens up many more possibilities for the configuration of action groups to adapt over time, as well as for collaboration between them. I’ve chosen to use the term “action group” rather than “affinity group” to emphasize that affinity exists in many different constellations, each with its own potential.
Recommended reading:
Trust is contextual — you may trust someone to be a good friend, but that is different from trusting them with your freedom. Deciding who to approach in your network should be based on trust that they can live with the possible consequences of their actions without betraying their comrades, even if it means a long prison sentence. Trust is qualitative in a way that can’t be reduced to a simplistic formula. It’s based on an intimate knowledge that can only come from singular experiences within a relationship. However, there are established practices for deepening trust that are still worthwhile.
Recommended reading:
Once there are two or three people who want to experiment with acting together, I recommend starting with actions that do not have particularly serious consequences if you get caught, such as breaking windows. This allows you to assess whether the configuration is a good fit, practice any skills that are new to anyone, establish operational approaches and a good “workflow” for the tasks involved, and develop an interpersonal dynamic that meets everyone’s needs, all in a relatively low-stakes environment. Progressively increasing the intensity of the action also gives you the opportunity to practice moving through fear so that decision-making, communication, and execution in high-stress situations can remain unimpeded.
“Operational security” means the practices that allow you to get away with crimes. I recommend that your action group first discuss each of the highlighted resources at the No Trace Project before taking action, in an outdoor and device-free location. Many of these discussions are well suited for larger affinity constellations than your action group. This will take a considerable amount of time, but an in-depth discussion of these topics will provide a necessary foundation. Don’t make the mistake of assuming that everyone is already on the same page. These conversations will also be an opportunity to discuss how you will prepare for any repression that may result from your actions.
With this foundation in place, you are now in a strong position to begin action planning. As you gain experience, organizing and executing actions will become much more natural. What was initially a lot to keep track of will eventually become second nature. This is another reason why it’s a good idea to start with actions that aren’t particularly risky.
Recommended reading:
Before your action group engages in actions that will be more intensively investigated, it is especially important that you become competent in two operational security practices:
DNA minimization protocols are necessary to avoid leaving evidence at a crime scene. However, these precautions are not perfect, so the action should be conducted in such a way as to leave nothing behind that could have DNA traces on it. I recommend learning and practicing this skill long before you actually need to use it for high-risk actions.
Recommended reading:
If there is no evidence left at crime scenes, and you have established practices that prevent targeted digital surveillance from providing leads, investigators will be forced to use physical surveillance to try to incriminate you. The main goal of physical surveillance is to surveil the suspect during an action (as they did for Jeff Luers), and if that doesn’t work, to surveil the suspect while they are preparing for an action (buying materials, doing reconnaissance, etc.), all the while mapping the suspect’s network to find more suspects.
Detecting physical surveillance is a skill that takes a lot of practice, so I recommend that you start learning it long before you actually need to use it for high-risk actions. If you are ever the target of an investigation, this is the only thing that will prevent the police from following you to an action or preparation for an action.
Recommended reading:
Of course, skills related to action techniques are also important. For example, there are many ways to start a fire. Some are better than others in terms of reliability and effectiveness, but your approach should always be adapted to the specific scenario (target, exit plan, expected response times, etc.). Whatever techniques you end up using, it’s important to stay open to innovation rather than limiting yourself to following a guide.
Action technique is also related to operational security: for example, if you decide that the incendiary device(s) need a delay, it’s critical to be very confident that the delay won’t fail, as this would leave evidence for investigators to take samples from. Thoroughly test its reliability under the same conditions, and build in redundancy by using multiple delays on each device. Depending on the circumstances and terrain, you may even want to make a plan for noticing if any fires don’t start, such as choosing an exit route that provides a line of sight and pausing along it until you see the light of the flames.
Recommended reading:
The next step in developing capacity for action requires going beyond one’s own group. This is where things get really interesting: coordination between autonomous groups allows them to accomplish far more than they could on their own, while their autonomy wards off hierarchy and centralization. Of course, conspiring with more people involves risk and must be balanced with the need for compartmentalization — the need-to-know principle can help here.
Affinity is the strongest foundation for a common project among these groups — while affinity within an action group is based on interpersonal experience, affinity between action groups is based more on affinity with the project than with each other. The long-term search for affinity beyond your action group is what makes this foundation possible. Informal organization can then grow between action groups, which is a model that has been experimented with since the ’70s. Informal organization is born and shaped by the pursuit of specific goals, such as preventing the construction of Cop City through diffuse sabotage. “It doesn’t have a name to defend or assert, only a project to bring about”.
This outline touches on what I think are the minimal steps necessary to develop a capacity for hard-hitting action, limited to the topic of acquiring skills. Much more is needed — learning other skills beyond this baseline, experimenting with informal organization while navigating its challenges, developing analyses to understand the changing terrain, studying the vulnerabilities of domination, and focusing on all the other aspects that contribute to sustaining and intensifying action.
Submitted Anonymously Over Email
Submitted Anonymously Over Email